Mixed IT Services
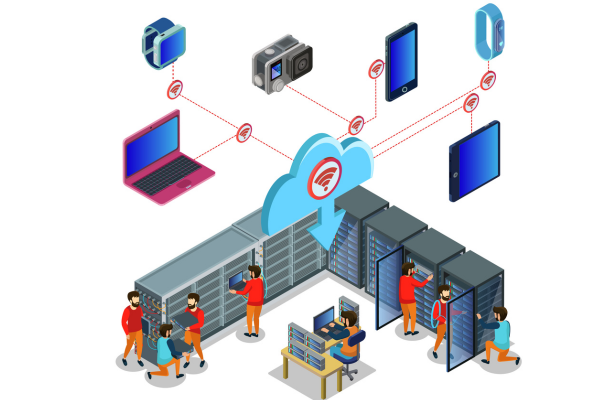
Revolutionize the enterprise utilizing peerless blended virtual services via NetraClouds.
Our Partners
























Transition with assurance utilizing our trustworthy blended technology offerings
Accelerate your digital modernization via mixed infrastructure systems provided by NetraClouds.
Boost Corporate Efficiency Via Our Mixed Technology Offerings
Receive personalized integrated cloud computing systems and construct a superior cloud infrastructure tailored for your enterprise.
Why select NetraClouds regarding converged technology services?
- Rapidly expand your operations to accommodate your company's changing requirements through tailored hybrid cloud computing solutions.
- Safeguard your digital atmosphere against online threats by partnering with a highly regarded hybrid IT system supplier.
- Decrease networking intricacies utilizing our bespoke hybrid cloud information technology offerings.
- Execute operational loads and acquire applications modified specifically to satisfy your firm's particular necessities.
- Acquire an all-inclusive and detailed strategy for your setting, irrespective of your underlying architecture.
Receive a custom quote for our Hybrid IT Services
What Our Clients Say
NetraClos Team provided the full solution for Fashion IQ, includes WiFi, perimeter security, music system and VOIP phone system. The whole team and after work support is amazing.
Discover the Advantages of Our Hybrid IT Services
Enterprises are implementing Desktop as a Service platforms with increasing speed since these interfaces are attainable via almost any gadget connected to the web. This implies that personnel can reach their virtual workstations irrespective of their physical location, an outcome recognized as highly valuable for the modern, largely telecommuting staff.
No Managed Detection and Response (MDR) framework is truly comprehensive without a dedicated unit of threat hunters actively scouring your ecosystem for adversaries, employing the complete spectrum of hunting methodologies:
Indicator of Compromise (IOC)-Based Threat Hunting: This constitutes the most elementary tier of threat hunting and is often the sole technique referenced by competitors. As a log-intensive strategy, it mandates that analysts examine records for specific identifiers, such as recognized malicious HASH values or IP addresses.
Tactics, Techniques, and Procedures (TTP)-Based Threat Hunting: This advanced practice requires the expertise of Tier 2 threat hunters or higher to adopt an adversarial mindset, seeking scenario-based evidence of intrusion throughout your network.
Digital Forensics and Incident Response (DFIR): We possess the capacity to scan and analyze volatile memory across over 1,000 devices per hour. This capability empowers us to proactively utilize hunting techniques that were previously rendered unfeasible by labor constraints, ensuring no potential threat remains concealed. Should any malicious process be executing or scheduled within your environment, our analysts are guaranteed to discover it.
Optimal protection, detection, and response capabilities rely on telemetry gathered from the network's most vulnerable entry point: the endpoint. Consequently, no Managed Detection and Response (MDR) strategy is truly comprehensive without this critical visibility. Conducting behavioral analysis and threat detection at the endpoint level represents one of the most effective defenses against ransomware and other malware, whether securing remote work environments or heavily fortified corporate networks.
NetraClouds has invested extensive resources in analyzing independent assessments and subjecting various Endpoint Detection and Response (EDR) platforms to rigorous testing by our elite penetration specialists, thereby sparing your organization the burden. This dedication has empowered us to establish an industry-leading, vendor-agnostic methodology that ensures the future resilience of our MDR program.
Our strategic EDR partners possess the capability to either supersede legacy signature-based antivirus solutions or facilitate the co-management of your current EDR infrastructure, seamlessly integrating it into our comprehensive MDR architecture.
Confirm Identity in Person
Through this multi-factor authentication system, your staff utilize biological scanners and flash drive safety tokens.
Universal Second Factor
The U2F protocol permits individuals to insert a tangible USB gadget into their computer equipment to safely enter their profiles and software. Referred to as a U2F verifier, the unit safeguards secret codes using an anti-tamper part identified as a secure element (SE).
Web Authentication
By using WebAuthn, businesses can supply their workforce with the simplest verification technique: thumbprints. Additionally, it confirms the physical attendance of the user during the sign-in moment.
our outstanding achievements
A Promising Digital Transformation
In our journey of continuous growth and innovation NetraClouds made a significant impact by staying at the forefront of technological advancements. As we celebrate these achievements, we remain committed to our vision of a world empowered by innovation.
Solutions
Successful Projects
Locations
Glorious Years


Expand Your Combined Digital Framework as Your Enterprise Develops
A major perk of a virtual computing atmosphere is the inherent capacity to adjust fluidly to your firm's evolving demands.
Utilizing a blended technological setup enables you to swiftly scale resources in either direction to accommodate dynamic commercial necessities.
Additionally, as your corporation progresses and digital requirements increase, our group will engineer personalized hybrid cloud strategies to maintain ongoing operational success.
Receive Candidate Profiles Delivered Straight to Your Email
Possess competency deficiencies? Submit your specifications, and our specialists will connect your organization with exceptional professionals customized to your requirements.s.
Protect Your Combined Tech Infrastructure Against Digital Dangers
Destructive programs and additional virtual hazards persist in spreading, often aiming at organizations functioning within cloud computing.
You will gain assurance recognizing that your cloud domain is comprehensively guarded by among the most esteemed hybrid IT foundation firms.
We intend to oversee your cloud surroundings, uncovering security gaps and striving to patch them immediately. We shall likewise discover dangers beforehand and remove them prior to their capacity to affect your enterprise.
Why Work With NetraClouds?
Your Questions Answered: Hybrid IT Services
Our hybrid IT frameworks deliver the adaptability and expandability required within the contemporary corporate landscape.
Collaborating with us allows our offerings to flawlessly merge internal hardware with virtual networks, permitting you to efficiently manage expenses versus output.
The nimbleness afforded by these mixed IT setups can propel your commercial expansion and inventive progress.
Safety constitutes a primary element of our mixed IT frameworks. We employ sophisticated defense protocols, featuring data encoding and multi-step verification, to shield your information throughout every system.
Our offerings supply the required safeguards to guarantee your hybrid IT setting stays protected against possible dangers.
Absolutely, at NetraClouds, we deeply understand that every enterprise stands as a unique unit, making generic approaches inappropriate.
Our hybrid IT tactics are carefully crafted to suit the specific demands of every customer. The final outcome creates a harmonious blend of local and internet-based infrastructure meant to enhance your corporate output, optimize spending, and strengthen protection.
While designing our hybrid IT systems, we place uninterrupted operations first.
By utilizing the backup capabilities and versatility found in both physical and cloud assets, we promise to sustain constant availability of your critical software and files, even amidst technical crashes or disasters.
Our dedication to you extends past the initial delivery of hybrid IT systems.
We offer all-day assistance via our group of skilled specialists. Be it a small glitch or a huge obstacle, our staff is always prepared to diagnose and fix difficulties, guaranteeing slight interference with your company functions.



















